SPF (Sender Policy Framework)
What Is SPF Record?
An SPF record is an email authentication record that can be published in DNS as a TXT record. It helps prevent spoofing and phishing by verifying the sender’s IP address against the return path address domain.
Where to configure?
To configure an SPF record, you need to modify your DNS records. For example, if you are using DNS providers like Godaddy, Hostinger, Hostgator, or NameCheap, you need to log in to your DNS manager and create a TXT record.
The SPF record will look something like this: v=spf1 <IP> <enforcement rule>
For instance: v=spf1 IP4:10.12.0.1 IP4: 192.168.12.1 -all
There are three enforcement rules:
- Hard fail (-all): When this rule is applied, the message is marked with “hard fail” and follows the receiving server’s spam policy.
- Soft fail (~all): When this rule is applied, the email is marked as “soft fail”. Typically, email servers are configured to deliver these messages anyway.
- Neutral (?all): This rule does nothing, i.e., it does not mark the message envelope. It’s usually reserved for testing purposes and is rarely used.
What these IP addresses are defined in SPF record: As said email will be verified based on Sender IP.
The IP addresses defined in the SPF record are the sender’s network Firewall IP, Application IP, or Connecting IP (last hope of sender network, which is a static IP address or public-facing IP).
How it works and how it checked the IP address?
Before email getting deliver to the sender mailbox Email filtering services like Office 365 check SPF before delivering emails to the recipient’s mailbox.

When SenderA@contoso.com sends an email to a user account at domain.com, e.g., recipient@365cloudit.com, Office 365 filtering or protection service checks for SPAM and email authentication before delivering the email to the recipient’s mailbox.
To check if the email is legitimate or not, the filtering service checks the SPF record against the return path of SenderA@contoso.com by contoso.com. To check the return path, you can look for the email header on https://mha.azurewebsites.net/. Paste the header and analyze it to search for the Return Path address.

This value should be same as FROM address.
Now Office 365 filtering/ spam check will send the query to domain to validate the IP address is present in the TXT record.
You can check the IP address in the header again for example:

What happens if the Sender IP address is not present or the Return path is different from the FROM ADDRESS?
If the IP address is not the same, then the filtering service treats the email as SPAM and increases the SCL value. This email will be delivered to the JUNK/SPAM folder of the user’s mailbox.
If the return path is not the same as the FROM address, then the email will be considered as spoofed and delivered to the JUNK/SPAM folder of the user’s mailbox.
What is the MAIL FROM and FROM address?
The 5321.MailFrom address, also known as MAIL FROM address, P1 sender, or envelope sender, is the email address recorded in the Return-Path header field in the message header.
The 5322.From address, also known as the FROM address or P2 sender, is the email address in the From header field of an email and is the sender’s email address that’s displayed in email clients.
Drawbacks of SPF:
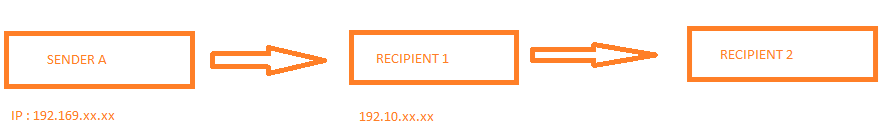
In the below image, Sender A sends an email with an IP address 192.168.xxx.xxx to Recipient 1. Now, Recipient 1 has forwarding configured to send email to Recipient 2.
In this case, when the SPF check is initiated from Recipient 2, it will send the query to Sender A’s domain based on the return path email address to check for the Connecting IP, which is 192.10.xx.xx (Recipient’s 1 IP). It is unlikely that Sender A would have Recipient 1’s IP address in their DNS record, and hence, SPF will fail, and the SCL value of the email will increase.